BSkyB has become the latest high-profile victim of a security blunder which has caused them to suspend all their Sky Android applications from the Google Play app store.
The hackers would appear to have used a combination of phishing and social engineering techniques to compromise a trusted computer and steal corporate login details for third-party sites such as Google and Twitter.
The storefront for Sky’s Android mobile apps was defaced, with the app descriptions changed and screenshots replaced.

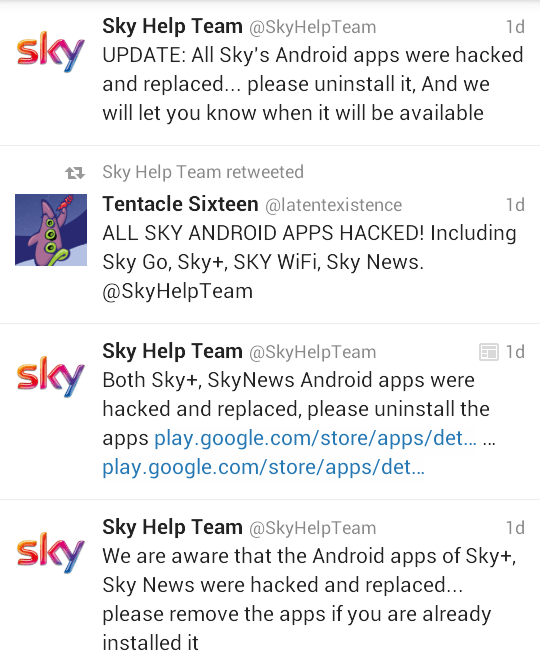
To make a bad situation even worse for Sky, one of their official Twitter accounts was also compromised and the hackers used it to draw more attention to their handywork.
Fuelled by the ‘official’ Twitter misinformation, customers were led to believe that the apps had also been tampered with, although this has been subsequently denied by Sky on their Help Forum:
We have temporarily removed our Apps from the Google Play store following a security alert.
All Sky Apps were unaffected and any Sky Android apps previously downloaded by customers are safe to use. There is no need to remove them from your android device.
As soon as we have restored the apps on Google Play we will post up an update.
In a related security breach, Twitter has locked access to @SkyHelpTeam, which is why we are currently unable to tweet from this account. However, help and info is available via @SkyHelpTeam1, Facebook and here on the Sky Help Forum.
The tweet that was made from the @SkyHelpTeam twitter, in the early hours of Sunday morning, advising customers to unistall their apps was NOT an official tweet from Sky. Twitter security immediately detected this vogue messaging and locked account as part of agreed standard security process.
Sky have suffered this humiliation as a result of sloppy security practices. With a robust security policy the damage from this attack could have be limited or prevented entirely.
My recommendations for an apps publishing security policy:
- Use a dedicated Google account for the Google Play Developer Console, not an account used for other Google services. Do not divulge the email address of this account.
- Enable 2-Step Verification on your Google account and use Google Authenticator to login. Make sure that you properly sign out of your Google account when you have finished each session.
- Only use a bookmarked https link to access the Developer Console. Never click on links contained in emails or on other web sites.
- Tightly limit access to the Developer account. Only permit access to those directly involved with apps publishing, usually just the Apps Manager and their deputy.
- Wherever possible use discrete private keys to sign each application – see the Signing Strategies section of Android Developer Tools. This limits the damage should the private key for an individual app be compromised.
- Store your signing keys securely, preferably using a hardware-encrypted USB flash drive (such as an IronKey). Physically store the keys in a locked safe.
- Use a standalone computer for code signing and never connect it to a network. Treat all networks as untrusted, even your corporate LAN.
- Have a well rehearsed contingency plan to ensure business continuity if the worst does happen.